Making a tar pit
Attack bots are everywhere, lets see what they want
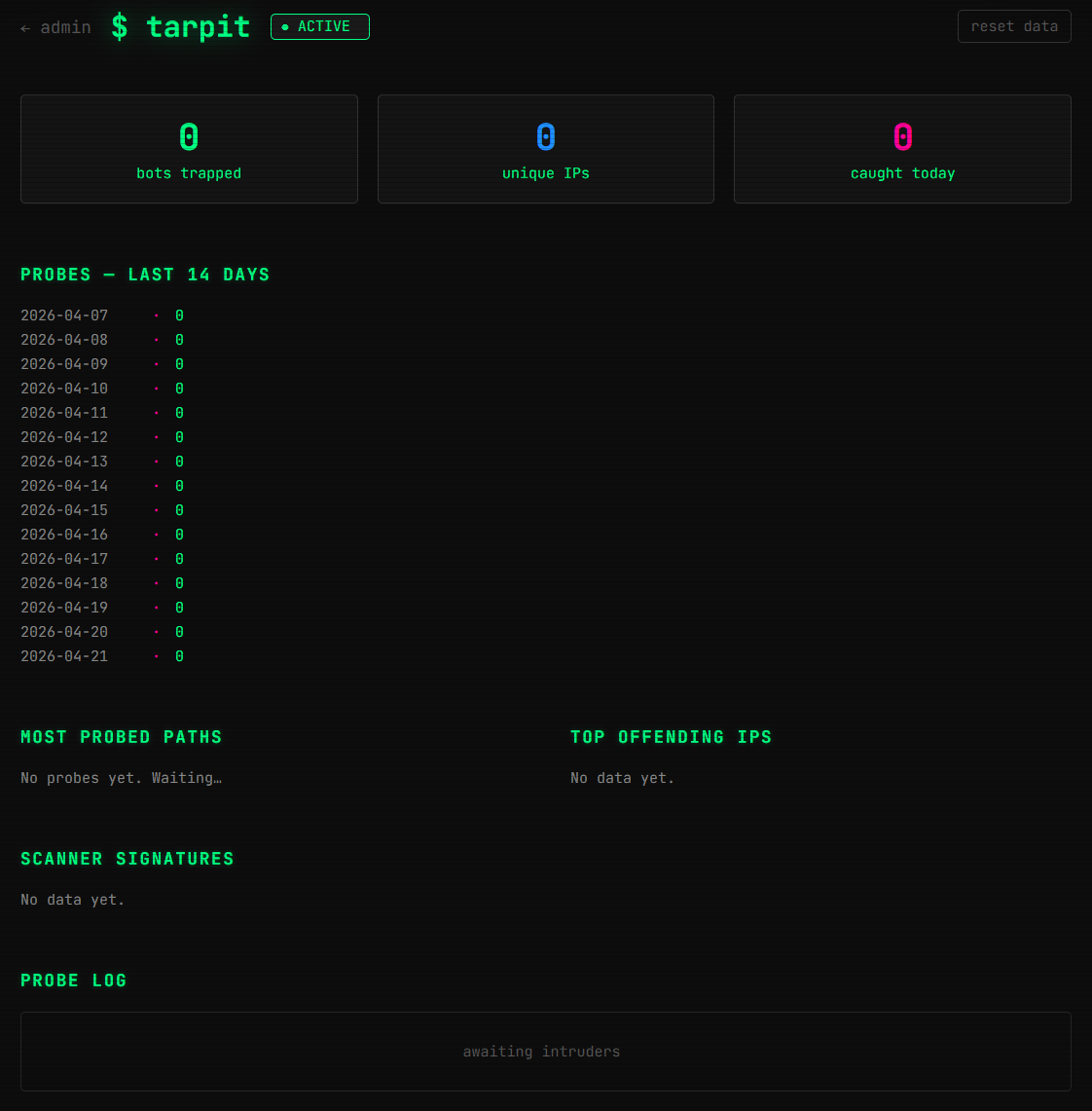
My analytics pages tend to look like this:
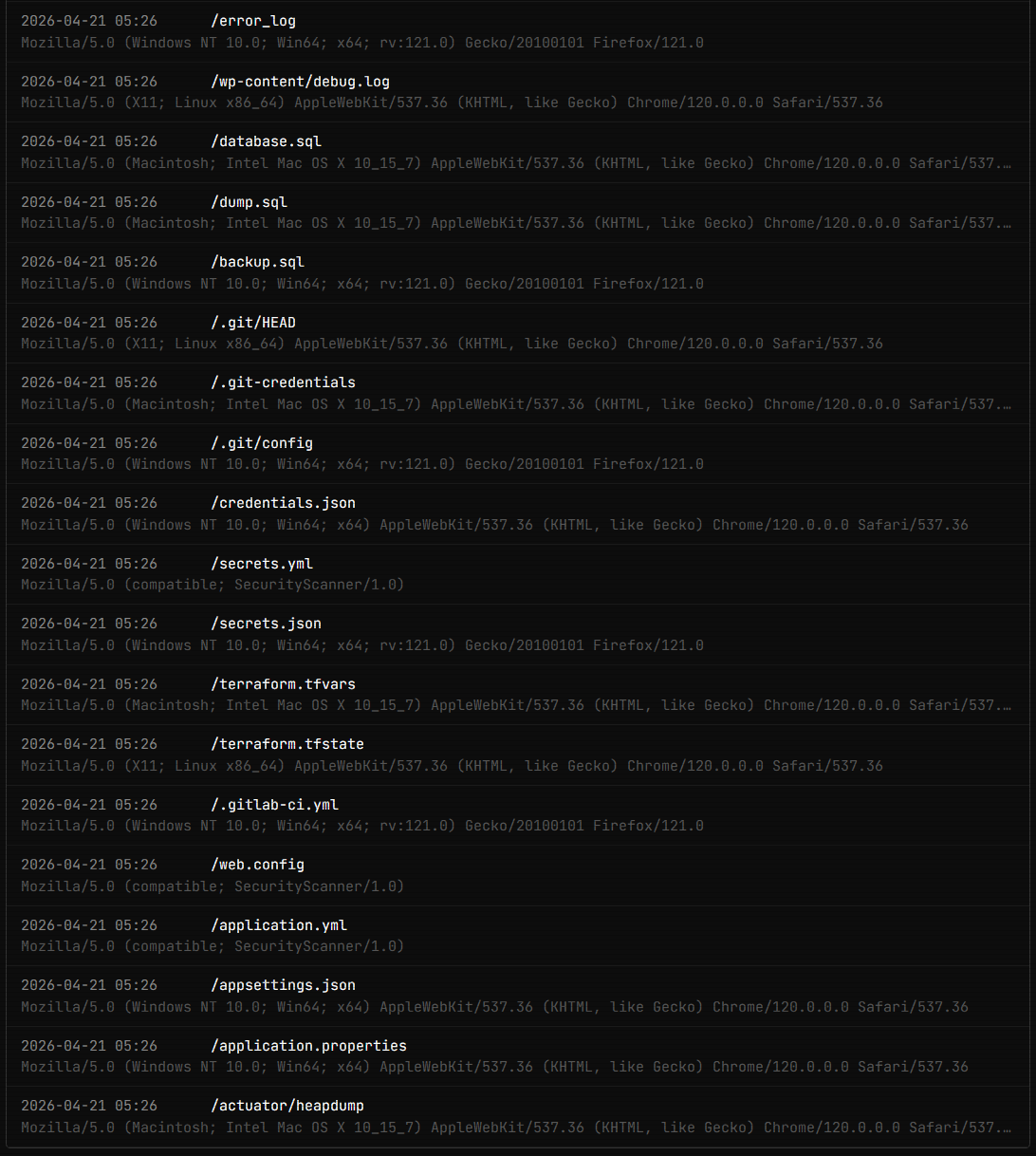
Those are automated scripts that crawl the internet looking for poorly configured web apps to take control of. Whether it is to gain access to the host system, overwrite the page with scam stuff, or gain access to API keys that give them "free" access to paid resources, they are up to no good.
There are a few ways to handle them at the expense of some server resources. - Slow Loris is a method that sends chunked HTML pages with a slow response time, a few bytes every few seconds. The intent is to hang the bot on a page and waste its time.
-
Dumping fake credentials on these paths can poison the attackers database and also cost time and lower value.
-
Infinite Mazes of HTML files that have links to other config files that are HTML files that have links to other config files that are HTML files that have links to other config files that are HTML files that have links to other config files that are HTML files that have links to other config files that are HTML files that have links to other config files that are HTML files... you get the point
-
A Tar Pit is a combination of those. It serves contextually appropriate fake content. .env paths get fake AWS/Stripe/DB credentials, SQL paths get a fake DB dump with fake password hashes, .git paths get fake config with a fake token, PHP paths get fake config includes. The drip streams 32 bytes every 3 seconds, so a ~1KB response holds the connection for ~90 seconds. Add logging to it and it gives me, the victim, a look at how well I am able to manage to waste their time.
Here is the page I have set up to track the tar pit: